In today's digital world, securing communications and ensuring the authenticity of identities are paramount. One of the core components that enable this level of security is digital certificates. These certificates are used in a variety of security protocols, such as SSL/TLS for secure web browsing, email encryption, VPN access, and more. Managing these certificates properly is crucial for maintaining data integrity, confidentiality, and trust across digital platforms. This is where certificate management comes into play.
In this article, we'll explore what certificate management is, why it's important, the processes involved, and how businesses can implement efficient certificate management strategies to protect their systems and data.
What is Certificate Management?
Certificate management refers to the lifecycle management of digital certificates within an organization. Digital certificates are used to authenticate the identity of entities (such as websites, users, devices, or applications) and enable secure communications through encryption. Proper certificate management ensures that these certificates are properly issued, renewed, deployed, monitored, and revoked when necessary.
A digital certificate typically contains the following information:
- The subject's public key.
- The identity of the certificate holder (such as a person or organization).
- The name of the certificate authority (CA) that issued the certificate.
- The certificate's validity period (start and expiration dates).
- Digital signatures used to verify the authenticity of the certificate.
Certificate management is essential for ensuring that these certificates continue to serve their purpose effectively and securely throughout their lifecycle.
Why is Certificate Management Important?
Effective certificate management is crucial for several reasons:
- Ensures Security and Trust: Digital certificates establish trust between entities (e.g., a website and a user) by confirming the identity of the entity and securing communications. Proper management prevents misuse, such as unauthorized access or impersonation.
- Maintains Regulatory Compliance: Many industries are subject to stringent data protection regulations (such as PCI-DSS, HIPAA, GDPR) that mandate the use of secure communication protocols, like HTTPS, which rely on certificates. Failure to manage certificates properly can lead to non-compliance and potential legal and financial repercussions.
- Prevents Data Breaches: Expired, revoked, or improperly issued certificates can expose organizations to attacks. Certificate management ensures that certificates are up-to-date and properly configured, reducing the risk of security vulnerabilities and breaches.
- Avoids Downtime: Expired certificates can cause disruptions in business operations, such as websites becoming inaccessible or communications being interrupted. Proactively managing certificate renewal and deployment ensures smooth, uninterrupted services.
- Streamlines Operations: Centralized certificate management allows for easier tracking, renewal, and revocation of certificates. This reduces the administrative burden and ensures a consistent security posture across the organization.
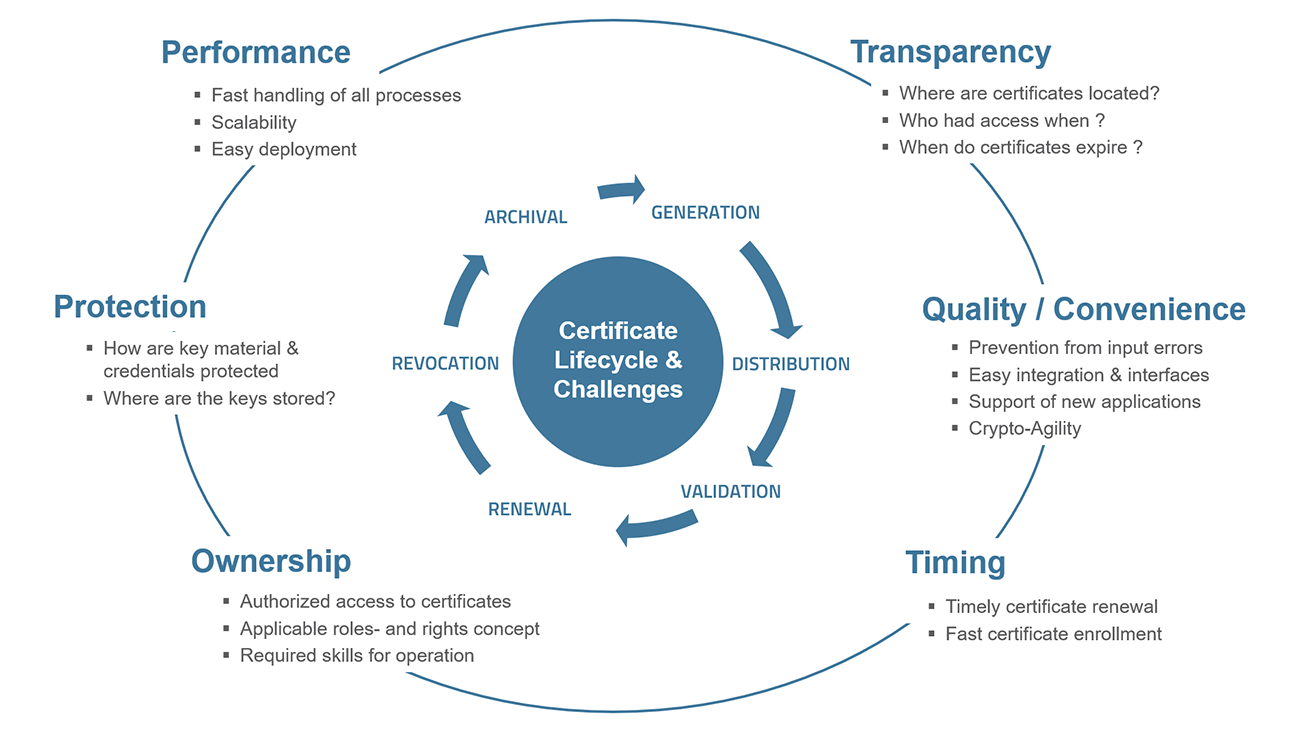
Key Processes Involved in Certificate Management
- Issuance: The process begins when a certificate is requested from a Certificate Authority (CA). The CA issues a digital certificate after validating the identity of the requester. The certificate contains a public key, which is used for encryption and digital signatures. In enterprise environments, an organization may set up an internal CA for issuing certificates to its own users and devices.
- Deployment: Once issued, the certificate must be deployed to the relevant systems, applications, and services that require secure communication. This may involve installing certificates on web servers, email clients, or network devices. For example, an SSL/TLS certificate needs to be installed on a web server to ensure secure HTTPS communication.
- Renewal: Digital certificates have a validity period, typically ranging from one to three years. Before a certificate expires, it must be renewed to continue functioning. Timely renewal is essential to avoid security vulnerabilities and prevent service disruptions. Automated systems can be set up to remind administrators when certificates are nearing expiration and manage the renewal process.
- Monitoring: Monitoring digital certificates is vital to ensure they remain valid and properly configured. This involves tracking the expiration dates, ensuring proper chain of trust, and confirming that certificates are installed on the correct systems. Monitoring tools can automatically alert administrators when certificates are about to expire, are revoked, or have invalid configurations.
- Revocation: Certificates can be revoked for various reasons, such as the compromise of private keys or an error in issuance. When a certificate is revoked, it is removed from the trusted certificate store and is no longer valid. The CA maintains a Certificate Revocation List (CRL), which contains all revoked certificates. Certificate validation systems, such as the Online Certificate Status Protocol (OCSP), check the revocation status of certificates in real-time.
- Storage: Proper storage of certificates and their associated private keys is critical for maintaining the security of the certificate. Keys should be securely stored, for example, in a Hardware Security Module (HSM) or key management system (KMS), to prevent unauthorized access or theft.
- Auditing: Regular auditing of certificate usage and management practices is necessary to ensure compliance with organizational policies and security standards. Audits help identify any misconfigurations, unused certificates, or potential risks.
Challenges in Certificate Management
- Scalability: As organizations grow and their IT infrastructure becomes more complex, managing certificates for thousands of devices, applications, and users can become difficult. Managing certificates in such large-scale environments requires automated solutions to ensure efficiency and reduce human error.
- Expiration and Revocation Management: Keeping track of certificate expiration dates and revocation statuses manually is time-consuming and error-prone. Failing to renew certificates on time can lead to service outages and security vulnerabilities.
- Lack of Visibility: Many organizations lack centralized visibility into their certificate management processes, making it difficult to track certificates across various departments and systems. This lack of visibility increases the risk of unmonitored certificates being misused or left outdated.
- Internal Certificate Authorities: Some organizations set up their own internal CAs for issuing certificates. While this gives organizations more control over their certificates, it can be challenging to manage and maintain a trusted internal CA, especially as the number of certificates increases.
- Legacy Systems: Older applications and systems may use outdated or unsupported cryptographic algorithms, making it difficult to manage and update certificates across the entire infrastructure. These legacy systems may not support modern encryption standards, leading to potential vulnerabilities.
Best Practices for Effective Certificate Management
- Centralized Certificate Management System: Implementing a centralized certificate management solution allows administrators to track, renew, and revoke certificates from a single interface. This streamlines operations, reduces the risk of missing expirations, and ensures consistency across the organization.
- Automation: Automating the certificate issuance, renewal, and deployment processes is essential for ensuring timely updates and reducing administrative overhead. Automation tools can send alerts for expiring certificates, automatically renew certificates, and deploy them across systems without manual intervention.
- Use Strong Encryption: Ensure that the digital certificates in use rely on strong encryption algorithms, such as SHA-256 for hashing and RSA 2048-bit or ECC (Elliptic Curve Cryptography) for public keys. Using strong encryption helps protect data and prevent attackers from decrypting it.
- Regular Audits: Conduct regular audits to ensure compliance with internal policies and external regulations. Audits help identify expired, revoked, or unused certificates, as well as misconfigurations that could lead to vulnerabilities.
- Security of Private Keys: Private keys should be stored securely, preferably in an HSM or KMS. They should never be exposed or transmitted insecurely, as their compromise can lead to identity theft or the ability to impersonate legitimate entities.
- Training and Awareness: Provide training for system administrators and staff on certificate management practices. Ensuring that everyone is aware of the importance of certificate security and the proper procedures for managing certificates helps reduce human error and strengthens the overall security posture.
Conclusion
Certificate management is a critical aspect of cybersecurity, ensuring that digital certificates remain secure and functional throughout their lifecycle. With effective certificate management, organizations can secure communications, authenticate identities, and maintain regulatory compliance, all while minimizing risks such as data breaches and service outages.
By implementing automated tools, centralizing management systems, and following best practices, businesses can streamline their certificate management processes and protect their data, networks, and systems from emerging threats. As organizations continue to evolve their IT infrastructures, certificate management will remain a key component in safeguarding digital communications and maintaining trust in the online world.